The Internet and social media platforms have kicked the doors wide open for child predators to hunt, lure, and groom victims online.
Every day there are at least 500,000 predators online. 1 in 5 children report they’ve been solicited or contacted by a predator in the last year.
Chances are a child you know has had this experience. It’s frightening to think about and terrifying for a child caught in a predator’s trap.
How do predators find children online?
Oftentimes children inadvertently fall into the traps set by predators. 46% of children give information away about themselves online – perfect tools for predators to use to identify victims, build trust and establish relationships around shared interests.
How it starts:
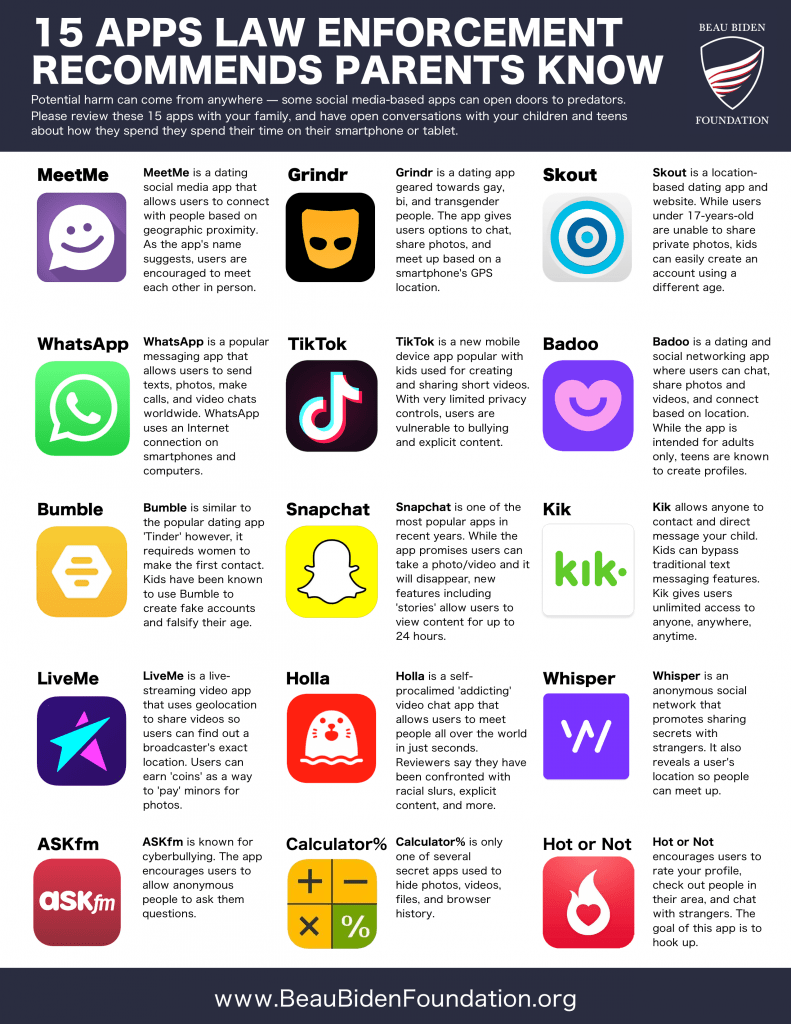
A predator targets a child in a public chat, on a social media platform or in an online game. The predator may comment on a social media post or send a direct message. To gain trust, predators will typically lie about their age – they may adopt a persona that’s just a bit older than the potential victim.
Predators then take the conversation further by asking more private questions, often in a different, more secretive app to test the child’s boundaries. Questions turn more personal, as they ask about other relationships the child has – with parents, friends, teachers, other adults. Predators use this information to build walls between a child and peers in their lives to further isolate them.
Conversations start innocently enough, and a predator may offer small tokens of appreciation, praise, or a willingness to listen at any hour. As the connection develops over time, the predator will offer the child small gifts – in the case of online gaming, the resources or currency used in the game. Perhaps it’s a gift card or something seemingly innocent the child may not be able to purchase themselves.
How it progresses:
The goal of the predator is to establish a secret or special relationship with the child – a relationship the child protects.
Once boundaries are tested, the bond is strengthened and the child protects the predator instead of themselves – the predator then begins to slowly sexualize the interactions with the child. As discussions turn sexual, the predators plays to a child’s natural curiosity about sexuality: the predators may share nude or partially nude images of themselves or of other children. Discussion around sexual activity primes the child for ongoing sexual conversations.
The predator will likely begin to ask for sexually explicit images and/or videos of the child.
Unfortunately, children will often share explicit images or videos of themselves – from partially clothed to fully nude.
* Once a child shares images and videos, the predator now has another form of control over a child: the predator threatens to share the images with parents or friends in order to force the child to provide more images and videos. This is known as sextortion – and it’s illegal.
The key here is power and control – online predators seek to exert control over their victims. From monopolizing the child’s time to shaming the child into providing explicit images, the predator moves the relationship from emotionally dependent to emotionally controlling and abusive.
Part II of this blog can be found here: www.BeauBidenFoundation.org/OnlinePredatorsBlog2.
Online Predators: What You Need To Know To Protect Your Child Today
Please click here to download our informative and FREE ebook.